Detect Botnets: Best Practices for Botnet Detection
Botnet detection techniques to mitigate bots on your website. Bad bots can cause DDoS attacks, brute forcing, account takeover, credential stuffing, scraping, chargebacks, and similar abusive behavior.
Setting Up Botnet Detection On Your Website & Apps
What is a botnet? Botnets are typically computers, servers, and internet devices whose security has been compromised. In simple layman terms, a botnet is a collection of bots that perform automated behavior to complete tasks as directed by a central node. The bot owner will typically use one computer or device as the “CnC”, “C&C”, or “C2” (Command and Control) server. Setting up a C2 server ensures that the bot owner can communicate with the “zombies” or “slaves” connected to a botnet through this C2 network.
Botnet detection is important for every company to prevent bot attacks and malicious behavior that could detrimentally affect brand reputation, customer trust, and even service availability. Devices and computers with security vulnerabilities, such as outdated software, open ports, and insecure systems, are often infected with various kinds of malware and viruses. 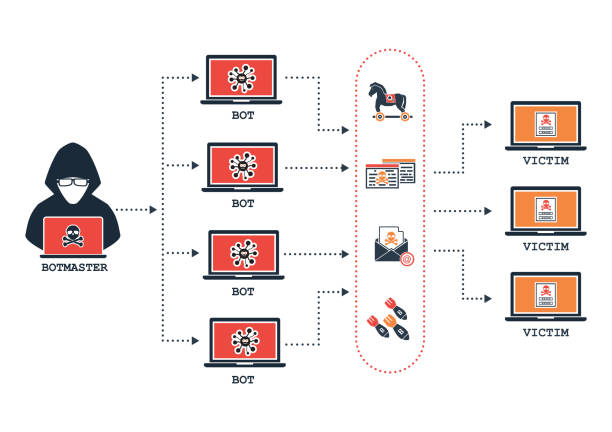
Malware enables hackers to perform malicious tasks through an infected user’s device and subsequently use their IP address. This keeps the identity of the fraudster or hack protected, and allows a cybercriminal to quickly gain access to a device or IP address in a country over 5000 miles away. Botnets affect all kinds of IoT (Internet of Things) devices, smartphones, laptops, computers, tablets, servers, and similar devices that are connected to the internet.
Cybercriminals take great measures to prevent their victims from knowing their devices and computers are infected. While it can be incredibly difficult to detect botnets, this guide will discuss techniques and tools for botnet detection.
Categorizing Botnets
Botnets are categorized according to the following criteria-Botnet Functionality.
- Botnet Architecture.
- Platform Targeting – Linux, Mac, or Windows.
- Abusive Behavior, such as are these connections being used for chargeback fraud, credential stuffing, fake accounts, bot scraping, brute forcing, account takeover, or similar abuse.
Let’s get into botnet mitigation, prevention, and detection.
Preventing Your Devices From Being Infected by Botnets
Botnet attacks can impact your business, cause API downtime, submit chargebacks, and may even scrape sensitive content from your website. Botnets can use their combined capacity to attack your entire IoT setup with various attacks like DDoS (Distributed Denial of Service), a distributed denial of service attack across your entire network.
To mitigate bots on your network, ensure your devices are protected with the latest updates and patches. Enabling a strong botnet detection algorithm which is regularly monitored and updated can also identify intrusions or possible viruses.
Malware detection software and real-time monitoring solutions should also be installed so that your devices, computers, and connected network are all protected. Malware scanning on your network should have a two-pronged analysis. First, performing a static analysis that scans for known malware signatures and then links to the botnet servers as malicious .exe or.bat files.
Secondly, an anti-malware software should analyze for changes in Windows host files; unfamiliar and unexpected processes; SMTP emails and traffic from SMTP; traffic from IRC through a specified range of ports; unexpected pop-ups; unwarranted messages and pop-ups; reduced performance of the devices and computers; or identical DNS requests that may also be simultaneous.
Bot Detection False Positives
In many cases, of course, preventing botnets on your own can cause false positives. It can be very difficult to distinguish between a single random attack and a truly well-concerted attack through a bot network. Sometimes even hackers use VPNs or proxies to mask their IP address identity – and may even teach their bots how to resemble real human behavior. This may look like there are many attackers at once, which may actually be generated from the same device. For example, some proxy services allow a single user to use multiple proxies.
Using a professional proxy detection solution can help clear up false-positives, by providing better confidence in detecting anonymized connections which allow users to tunnel in and change their IP address.
Why it is Difficult to Detect a Botnet?
Botnets do not have any specific identifiers or templates. Each botnet is unique based on how it has been created, what it has been set up for, how it has been set up, how it is meant to grow and multiply, why it was created and so many more factors. Although most botnets are created and communicated across a C2, many are also controlled on a P2P (peer-to-peer) design. Botnets are created and deployed with various motives. Some are meant to perform DDoS attacks and credential stuffing attacks, while others are meant to mine cryptocurrencies.
Bad bots can also use residential proxies and mobile proxy networks to make their requests look as legitimate as possible. This would produce very human-like traffic that’s hard to detect without a real-time API solution.
Botnets can be downloaded via email attachments, pop-up ads, and similar programs. Typically they are either .exe or .bat files. And in most cases, they are meant to infect your devices and computers and the network they are on. These are common entry points for most botnets, although they can also be embedded within mobile apps and even popular free software. Keeping your network up-to-date with all available updates and patches is a great way to mitigate vulnerabilities that botnets could abuse.
How to Protect Your Website Against Botnet Attacks
As the number of IoT devices increases, so will the number of botnets – in both numbers and scale. Since botnets can control thousands of devices at once, they are the ideal source for powering distributed denial of services attacks (DDoS). DDoS attacks can affect your entire business architecture and limit service availability for your customers. Attacks may be of two types:
- An Application Layer Attack is an attack where particular modules of an application or service are targeted.
- A Volumetric Attack, on the other hand, may flood your entire network or create excess requests across your transport layers.
In either case, the main motive of any DDoS attack is to ensure that your mobile apps, APIs, and websites are unavailable. Of course, nowadays, botnets are being used for brute forcing, account takeover, credential stuffing, and even chargebacks & payment fraud. Such attacks can damage your reputation and cause your customers to lose trust in your brand.
Instantly Block Bots & Mitigate Botnet Traffic
Protective Measures to Detect Botnets
To detect botnets and apply protective measures place two things must be done:
- Monitor failed login attempts to identify spikes and regulate the baseline of failed login attempts.
- Monitor the traffic across your network for any unusual activities and spikes or drops in traffic.
These methods are good ways to mitigate any botnet attack. Of course, there are other ways, like Honeypot and WAF rules that can also enhance bot detection, but botnets today are advanced enough to bypass both these methods.
Botnet Detection For Your Website
Detecting botnets on your website can be improved by looking for patterns of the device or request. Botnets will usually make simultaneous requests, or multiple requests within a very short period of time. Often you detect botnets by analyzing the request’s user agent and user language. While some browsers can be very popular, botnets will usually use languages and user agents that are more unique. This can help identify traffic strange patterns of traffic that doesn’t fit the profile of your normal audience.
Botnets typically like to attack specific pages, so you may be able to narrow down logs and analysis to certain pages with higher traffic on your website. To provide complete bot mitigation, it is best to perform analysis on the IP reputation to determine if the IP address has recently been engaged in botnet activity or abusive behavior.
Device behavior analysis with tools like a device fingerprinting solution can also identify requests made from the same device, even when the requests are tunneled through a proxy or botnet connection. Device Fingerprinting with JavaScript can identify non-human behavior, location spoofing, and automated requests which would all indicate risky behavior to help prevent botnets from attacking your websites.
How Dangerous Are Botnets?
Distributed Denial of Service attacks can be very dangerous. They can completely disrupt the process of an entire organization affecting almost every computer or server on the network, denying your customers access to your websites and apps. Botnets can easily perform highly coordinated behavior simultaneously from thousands of devices, which can perform detrimental actions at a significant scale.
The biggest fear is that botnets can auto generate if they have wormable properties and enslave other devices on a network. It can be an endless game to prevent botnet attacks on your own, without a cloud solution or real-time API for filtering high risk bots.
Are Botnets Illegal?
Since botnets are nothing but a network of computers that work independently, there is nothing quite illegal about creating a botnet. What is illegal is to install any kind of unwanted software or malware on a device that you do not possess. Thus, although many researchers make several botnets to test out processes and establish security systems, it is not illegal to create botnets.
Botnet Identification
Identifying botnets is extremely crucial to saving the integrity of your brand or business. Bots and proxies can cause a threat to your reputation and customers and severely impact your customer accounts and service availability. Many organized botnets function under the hood and often resemble human-like behavior and natural traffic patterns. It’s important for any company to have a plan to stop botnets. Beyond, DDOS attacks and brute forcing, botnet attacks can also be used to submit fraudulent payments, create fake accounts, or submit stolen user data from online breaches through methods like account takeover and credential stuffing.
While it is quite cumbersome to detect botnets, having the right tools ready and a robust support system to defend your network from botnets is crucial. Follow your logs, analyze your network and employ a cloud solution like IPQS to keep your company protected.
Share this article